According to the developers, WhatsApp guarantees complete security of its users' data. End-to-end encryption algorithms are used when sending messages therefore the source text can only be read by the participants of conversation. For the third parties, this information is converted into a set of incoherent characters. In fact, this statement is nothing more than a marketing ploy. Government organizations of the most countries have keys for message decryption, and user backups give full access to their activity history.
But it's not just decryptor keys that allow you to hack someone's WhatsApp. One of the main vulnerabilities of the messenger is two-factor authentication. Today, to get access to the subscriber's mobile network, you only need a powerful equipment and knowledge in the area that allows you create a single-purpose software. Special software redirects incoming messages of the target user and requests password recovery by phone number just to get a one-time password to log in to the account. One of the available tools that allows you to not only log in to someone's profile, but also download the activity history of a hacked WhatsApp account — WhaSpy. It is a very efficient tool. The use of two-factor authentication vulnerability rarely fails, it allows a user to access the target profile worldwide.
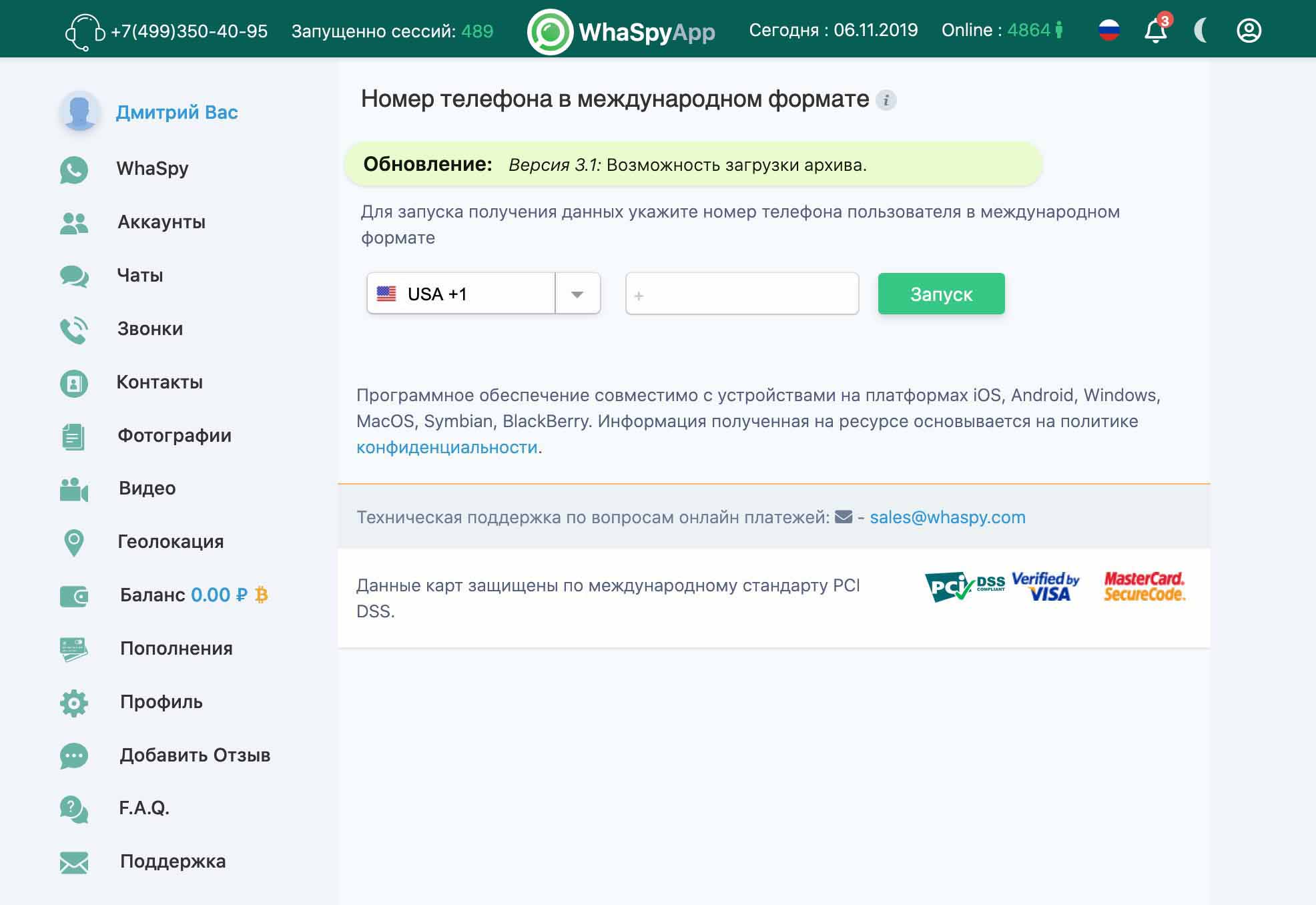
Step 1. Launching a SessionHaving registered at our website, you are automatically redirected to your personal account. Here you just need to specify the subscriber's number and click the button Get Data.
After successful completion of the session, all collected data will be visible on your personal account. You can access obtained data at any time.
How to Hack WhatsApp So That a Person Doesn't Find Out About It
Remote hacking of the messenger is performed discreetly and goes unnoticed for the account owner. The only way to find out about hacking is to view the number of active sessions at a time of gaining access. But WhatsApp users almost never pay attention to this feature.
You can also compromise yourself by being active in the messenger on behalf of the target user:
- Deleting or adding new personal or group chats
- Sending media files or deleting received ones
- Messaging the participants of active conversations
If you want to maintain complete anonymity, don't use regular payment tools for purchases such as bank cards or verified e-wallets. Nowadays, the only way to maintain confidentiality when transferring funds is to use cryptocurrency. You can use one of the following trusted services to buy it: LocalBitcoins & BestChange.
You should also protect any data transferred from your side:
- Use complex passwords for authorization.
- Connect to public Wi-Fi networks only via VPN.
- Create a new email account for signing up and don't use it anywhere else.
- Don't save passwords in the browser and exit the program after completing every session.
- Delete cookies and clear your browser history.
In this case, even if someone gets access to your devices, s/he won't be able to track your network activity and restore your actions.
How to Read Someone's WhatsApp from an iPhone
iCloud and iTunes features allow you to restore even deleted conversations, but you need to get physical access to the device with the target account. You can hack someone's WhatsApp from an iPhone without access to the gadgets of the profile owner in another way.
WhaSpy is a cross-platform application that doesn't care what device you are launching it on. Unlike iCloud and iTunes, the program doesn't download a backup copy to the device deleting all the latest activity, but collects current target data and provides it on a third-party platform. It allows you to not only get the latest information, but perform it completely unnoticed by the profile owner. The entire process, regardless of your operating system, is similar to the one presented above.
